While efficient, Suricata can be resource-intensive. A production environment typically requires at least 4–8GB of RAM and two CPUs. Suricata vs Zeek - Stamus Networks
Passive monitoring that alerts you to suspicious activity based on a standard signature language without interrupting traffic flow.
Threats evolve daily; using resources like the Emerging Threats Suricata ruleset ensures the engine can recognize the latest malicious signatures. SirCat's Tools
Suricata is a high-performance, open-source , Intrusion Prevention System (IPS) , and Network Security Monitoring (NSM) tool. Developed by the Open Information Security Foundation (OISF) , it is designed to analyze network traffic with "laser focus" to identify and block threats like malware, phishing, and unauthorized access. Primary Roles & Modes
Active defense where the tool is placed "inline" to block malicious traffic automatically, dropping packets or resetting suspicious connections. While efficient, Suricata can be resource-intensive
Unlike many competitors (such as Snort), Suricata natively uses multiple CPU cores simultaneously. This allows it to process high volumes of multi-gigabit traffic without sacrificing performance.
Generates detailed logs for protocols (HTTP, DNS, TLS), flow data, and file extractions, making it a powerful tool for post-incident forensics. Key Features Threats evolve daily; using resources like the Emerging
Suricata outputs data in industry-standard JSON formats (the "Eve" log), which allows for easy integration with SIEM platforms like Logstash , Splunk, and Elasticsearch. Implementation Best Practices
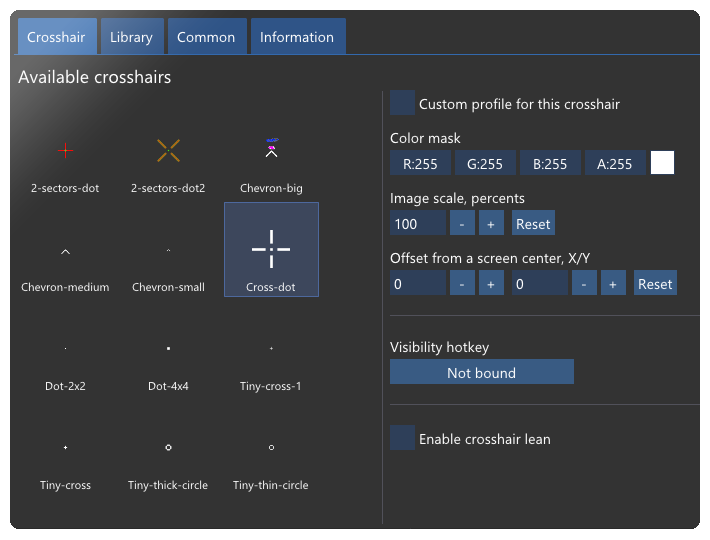
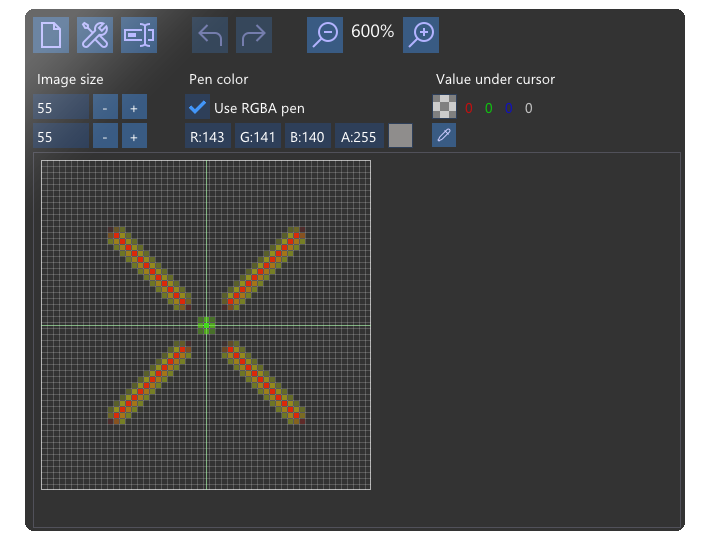
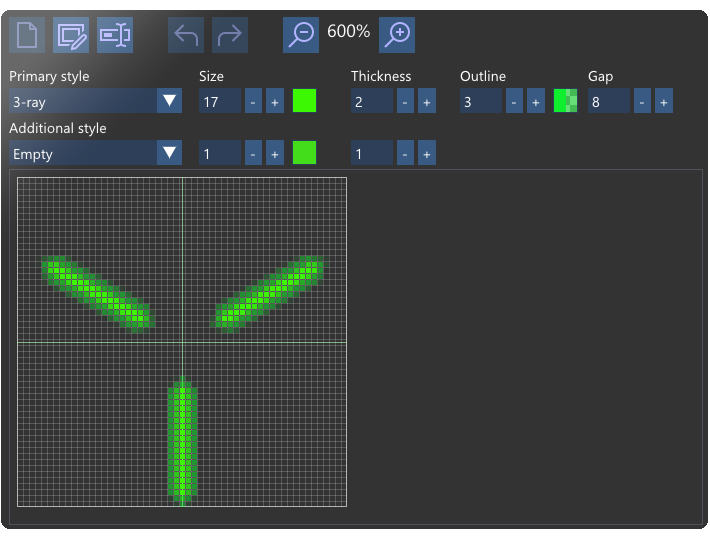
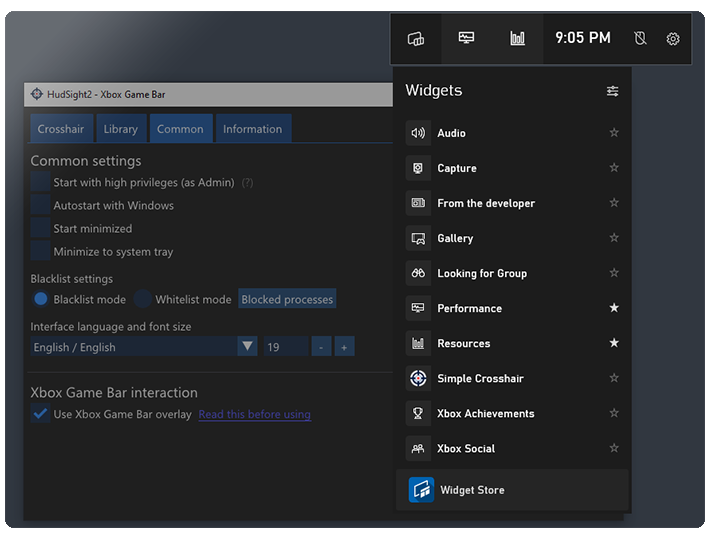
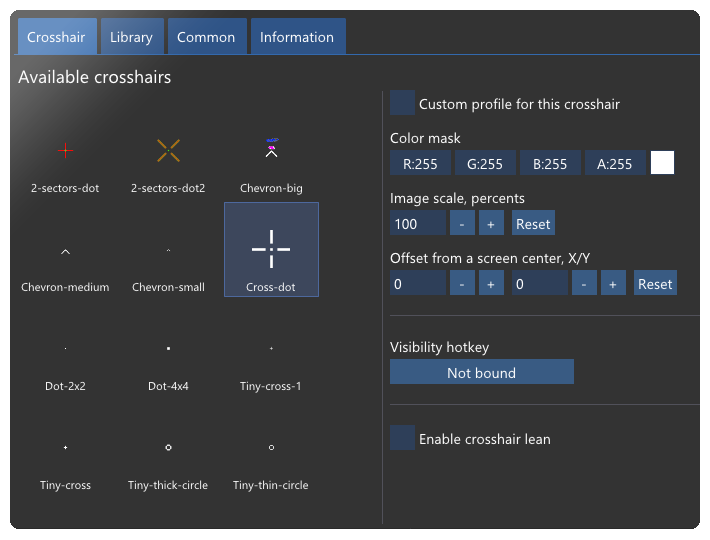
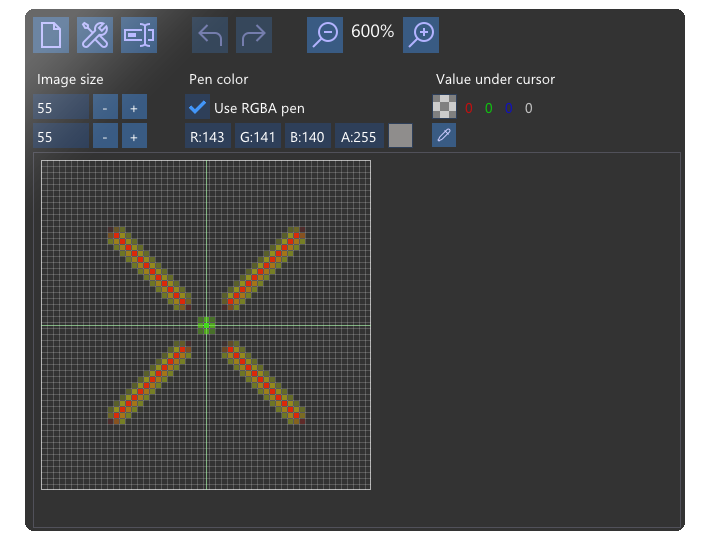
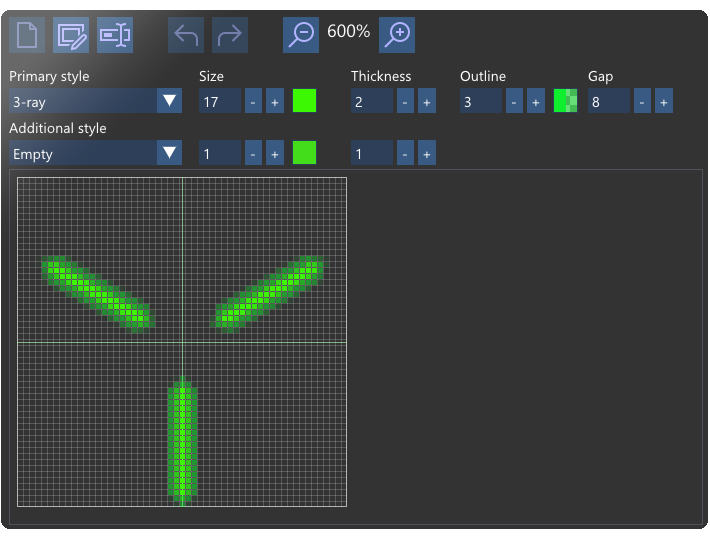
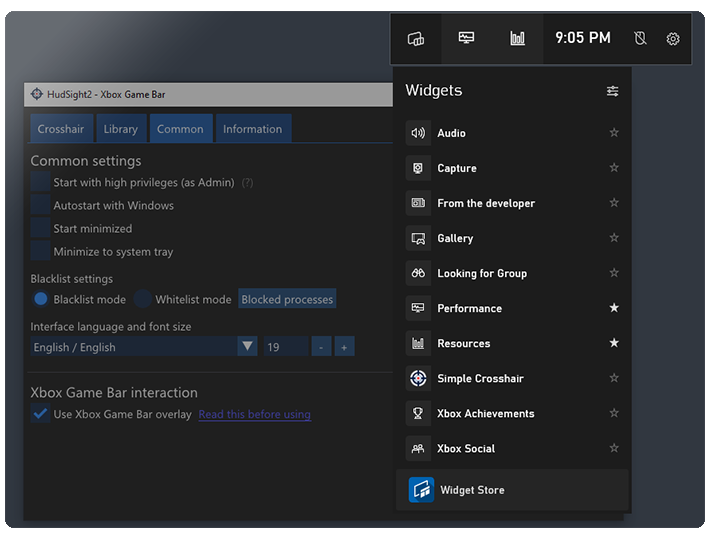
All updates are free!
Use Windows 10 and have a bit of free RAM and HDD space ;)
Just purchase the license and you'll get the code to your email right after your order is completed. Click to the activation button in the main software window or in the trial window and enter your code. Please note, the program requires access to the hudsight.com server to activate itself.
HudSight is not a cheat, it doesn't change games files or game play, it just draws an overlay (like Steam or Origin services or some other tools). But please make sure that the Terms of Service of a game you play do not deny such enhancement. For example, PunkBuster anti-cheat service gave manual bans for the screenshots of custom crosshairs in old Battlefield 2 and 2142 games.
Check our support area here