

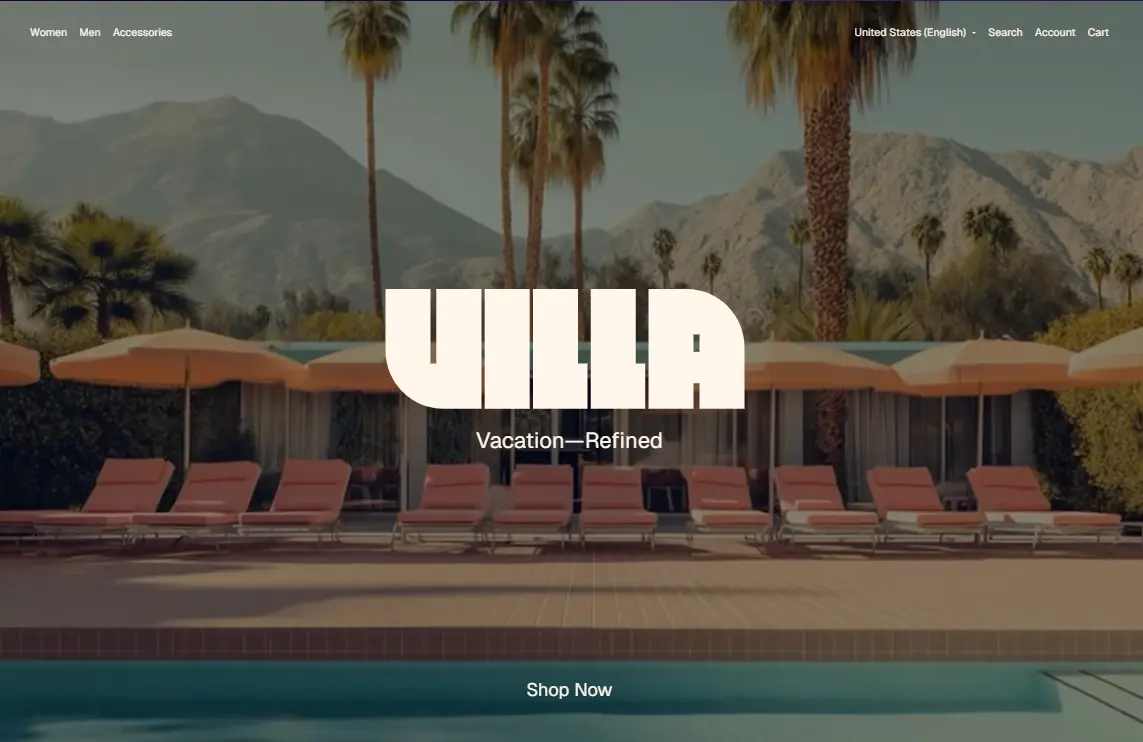
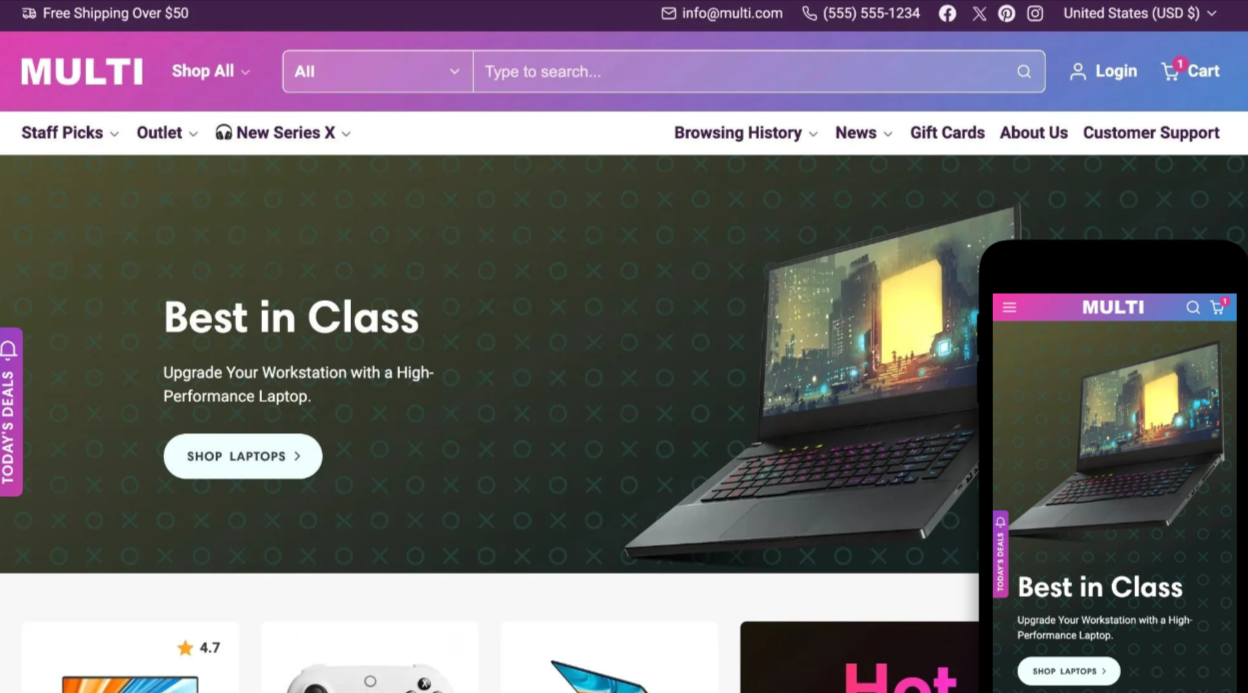
Horizon Shopify Theme
For a deep dive into how this specific type of threat operates, the following research papers and technical analyses provide the best insights:
: If you are looking for raw sandbox data, the entry for similar samples on MalwareBazaar or Joe Sandbox shows the exact behavior of the executable inside the ZIP, including network callbacks and file mutations [4, 6].
"book_PC.zip" is a known malicious file often associated with or similar information-stealing malware campaigns [1, 2]. These files are typically distributed via phishing or "SEO poisoning" on sites offering free software or PDF downloads [3, 4].
: You can find broader academic papers on Google Scholar that discuss the evolution of C++ based stealers and the use of ZIP file lures in modern cybercrime [5].
: Detailed reports by Sekoia.io or Any.Run examine the underlying code often packaged in archives like "book_PC.zip" [1, 3]. They cover its ability to exfiltrate browser data, crypto wallets, and login credentials [2, 3].
: If you have this file on your machine, do not extract it. It is designed to harvest your personal data and send it to a remote command-and-control server [1, 2].

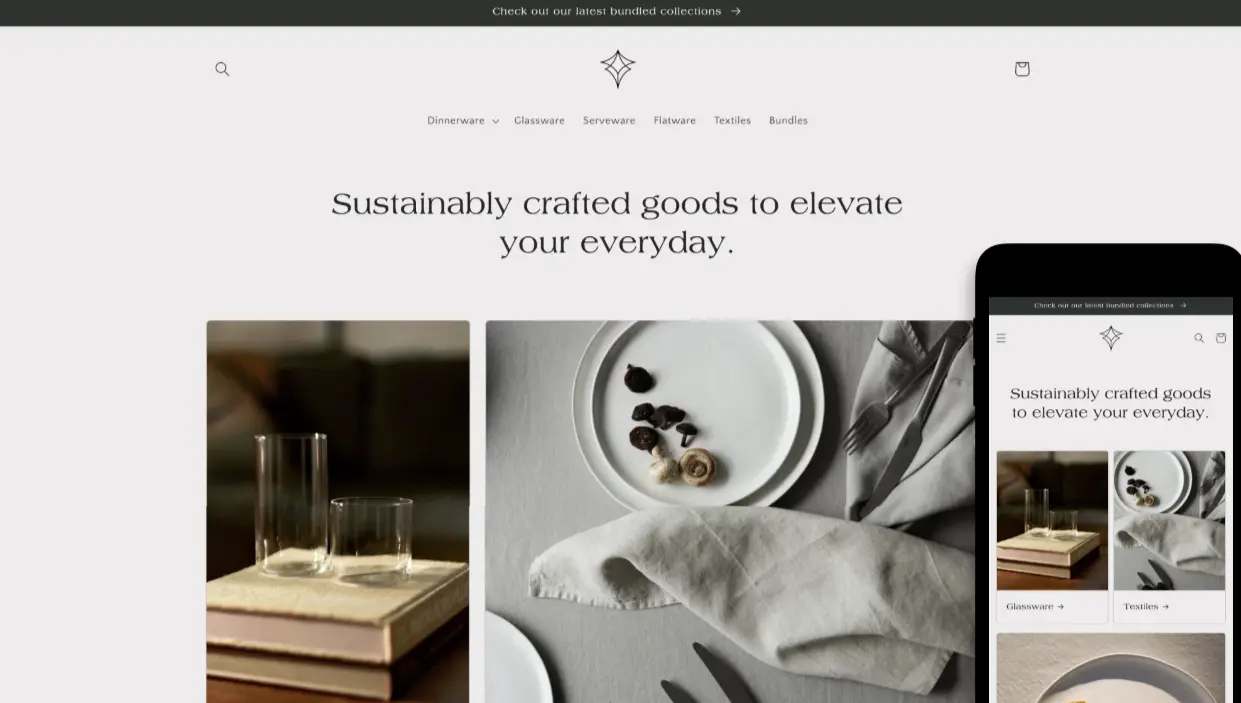
Horizon Shopify Theme

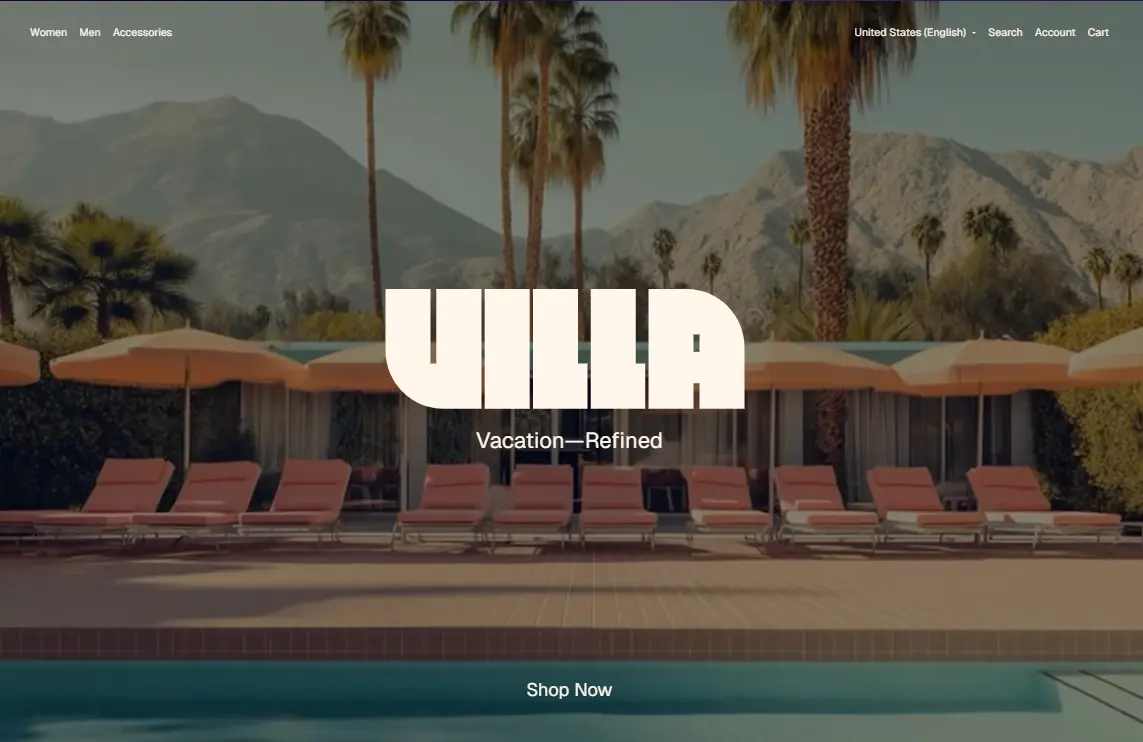
Dawn Shopify Theme

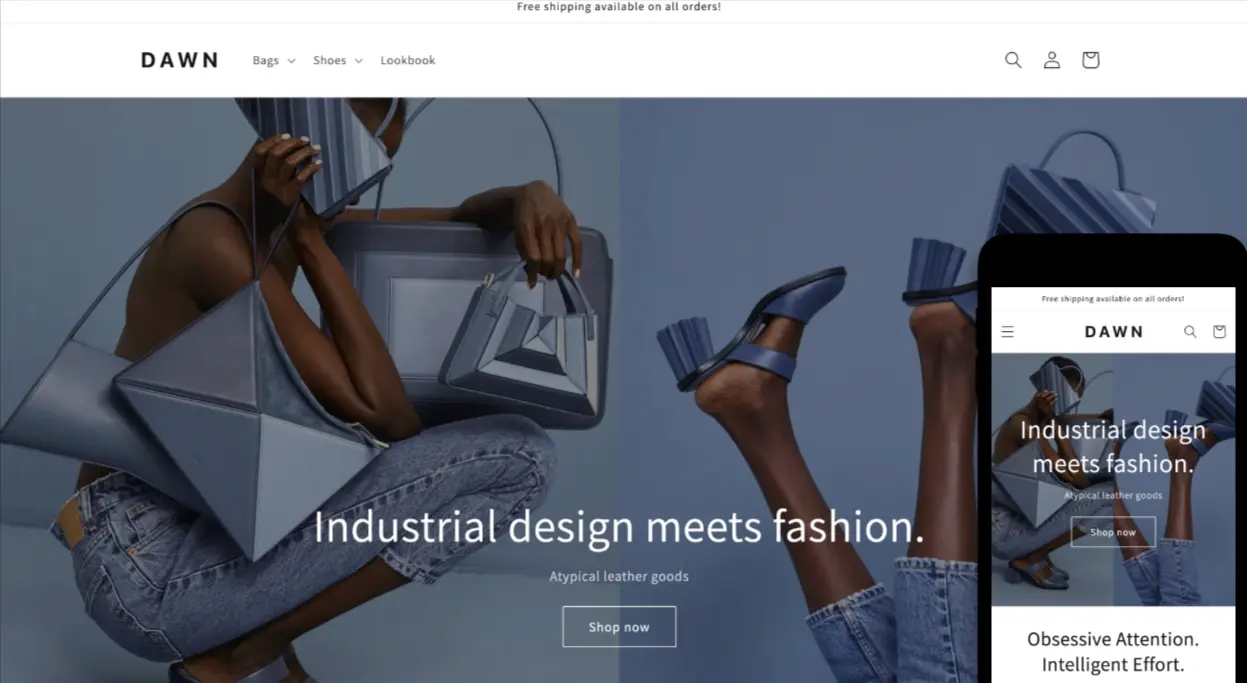
Spotlight Shopify Theme

Craft Shopify Theme

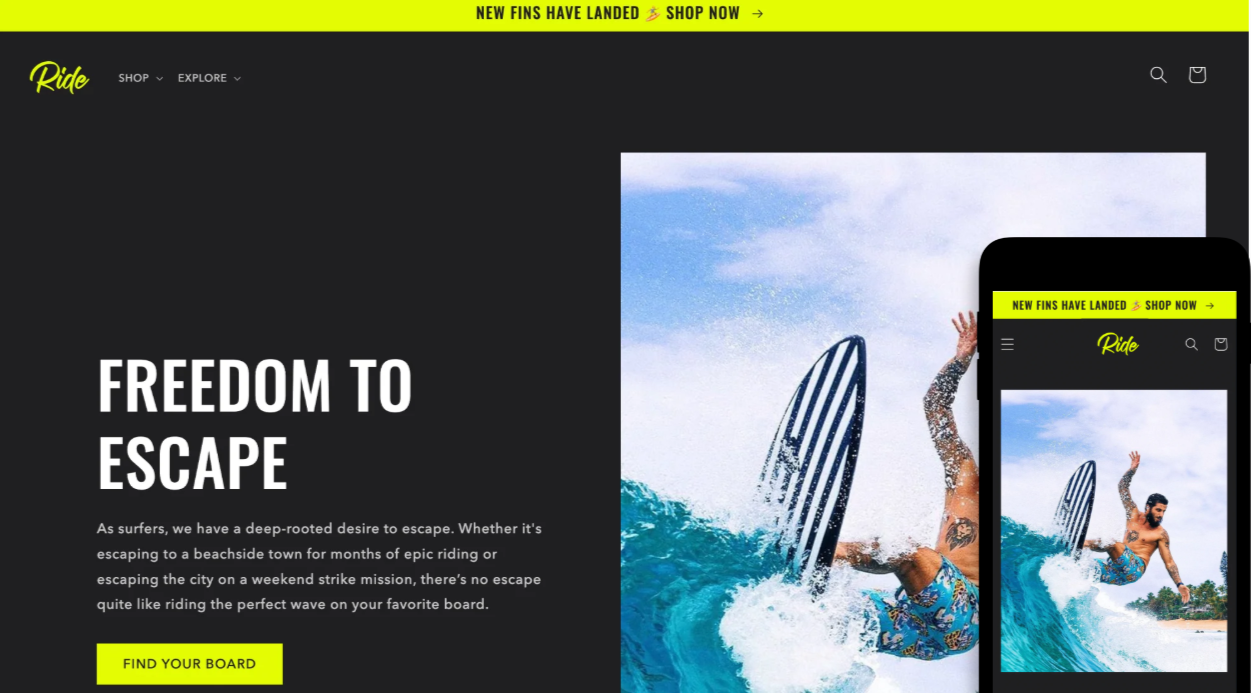
Ride Shopify Theme

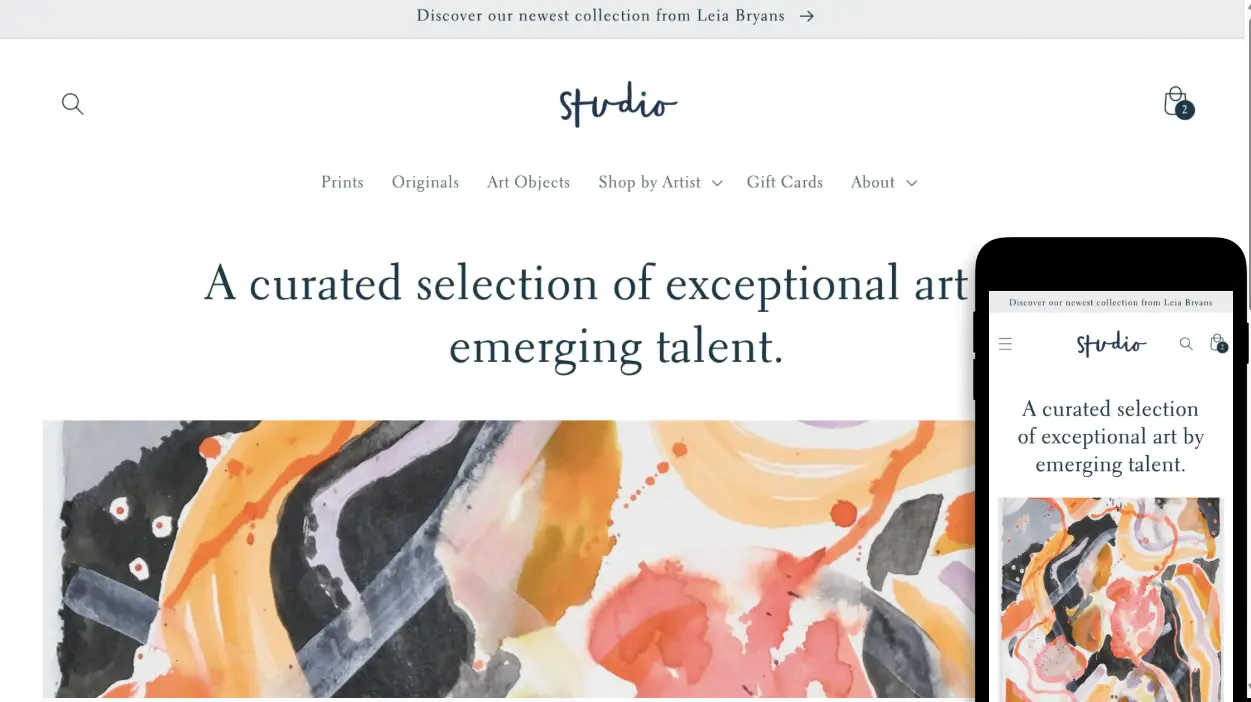
Studio Shopify Theme

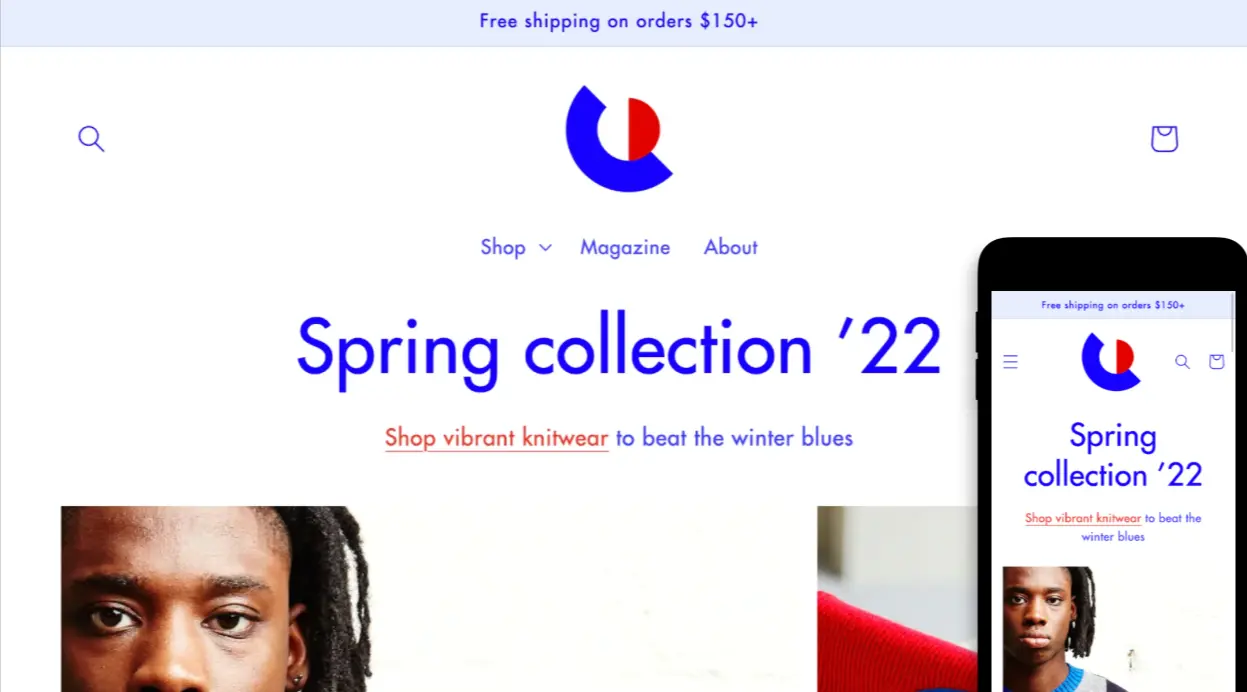
ColorBlock Shopify Theme

Multifly Shopify Theme
Further Reading
For a deep dive into how this specific type of threat operates, the following research papers and technical analyses provide the best insights:
: If you are looking for raw sandbox data, the entry for similar samples on MalwareBazaar or Joe Sandbox shows the exact behavior of the executable inside the ZIP, including network callbacks and file mutations [4, 6]. book_PC.zip
"book_PC.zip" is a known malicious file often associated with or similar information-stealing malware campaigns [1, 2]. These files are typically distributed via phishing or "SEO poisoning" on sites offering free software or PDF downloads [3, 4]. For a deep dive into how this specific
: You can find broader academic papers on Google Scholar that discuss the evolution of C++ based stealers and the use of ZIP file lures in modern cybercrime [5]. : You can find broader academic papers on
: Detailed reports by Sekoia.io or Any.Run examine the underlying code often packaged in archives like "book_PC.zip" [1, 3]. They cover its ability to exfiltrate browser data, crypto wallets, and login credentials [2, 3].
: If you have this file on your machine, do not extract it. It is designed to harvest your personal data and send it to a remote command-and-control server [1, 2].