





Supports switching to any rear and front cameras, with manual controls for every camera.
With 10 composition grid overlays and 9 crop guides, combinable with each other.
Fast and simultaneous capture in JPEG and DNG formats, for complete flexibility in post-processing.
Zoom with pinch gesture, by using the shutter button as zoom rocker or use the volume keys!
The exposure compensation is always available by swiping on the viewfinder.
Many options like shutter, zoom, exposure, white balance or camera switching are assignable to the volume keys.
Furthermore, there is the issue of . According to the World Bank, over one billion people globally lack formal identification. Without PoI, these individuals are "invisible" to the state, unable to vote, own property, or receive legal protection. Bridging this "identity gap" is essential for global economic development. Conclusion
However, the dawn of the internet shifted the landscape. Physical IDs are often impractical for the digital economy, leading to the rise of Digital Identity. This transition introduced new methods of proof, such as biometrics (fingerprints and facial recognition), two-factor authentication (2FA), and digital certificates. The Pillars of Modern Identity
The most secure systems, often referred to as "Multi-Factor Authentication," combine these pillars to ensure that even if one element is compromised, the identity remains protected. Challenges: Security vs. Privacy
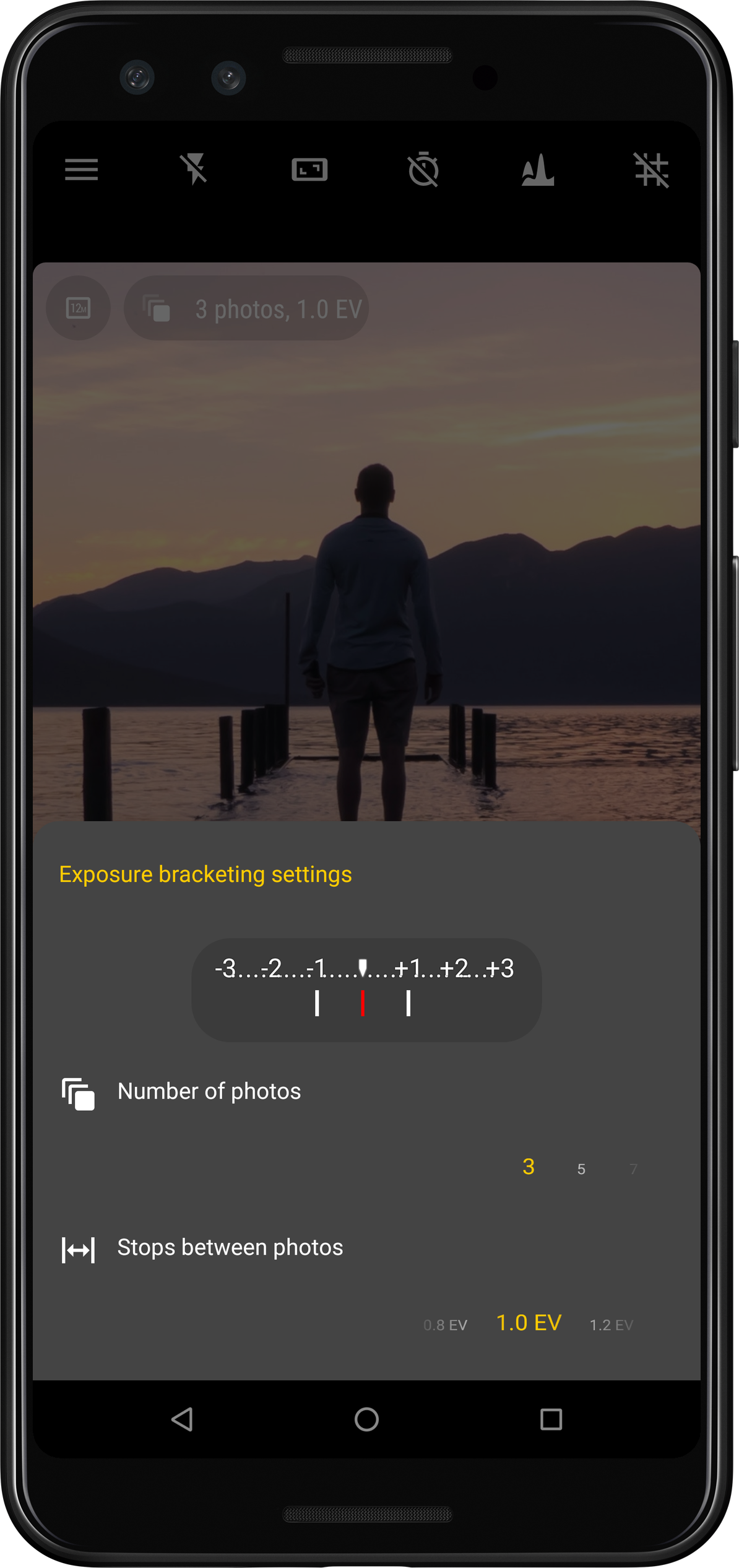
Take photos with multiple different exposures automatically.
New in version 5Now supports instantaneous capture even with JPEG+DNG on thousands of devices!

Capture picture series at regular intervals automatically (for instance timelapses or slow moving scenes)

Furthermore, there is the issue of . According to the World Bank, over one billion people globally lack formal identification. Without PoI, these individuals are "invisible" to the state, unable to vote, own property, or receive legal protection. Bridging this "identity gap" is essential for global economic development. Conclusion
However, the dawn of the internet shifted the landscape. Physical IDs are often impractical for the digital economy, leading to the rise of Digital Identity. This transition introduced new methods of proof, such as biometrics (fingerprints and facial recognition), two-factor authentication (2FA), and digital certificates. The Pillars of Modern Identity
The most secure systems, often referred to as "Multi-Factor Authentication," combine these pillars to ensure that even if one element is compromised, the identity remains protected. Challenges: Security vs. Privacy
